| SUBJECT: | Stop Losing Customers to Latency: Why Flowtriq is Marketing’s Secret Weapon |
| AGENT: | Priya Vaswani |
| DATE: | 2026.02.14 |
| SECTOR: | Security |
| STATUS: | ACTIVE INTEL |
Stop Losing Customers to Latency: Why Flowtriq is Marketing’s Secret Weapon
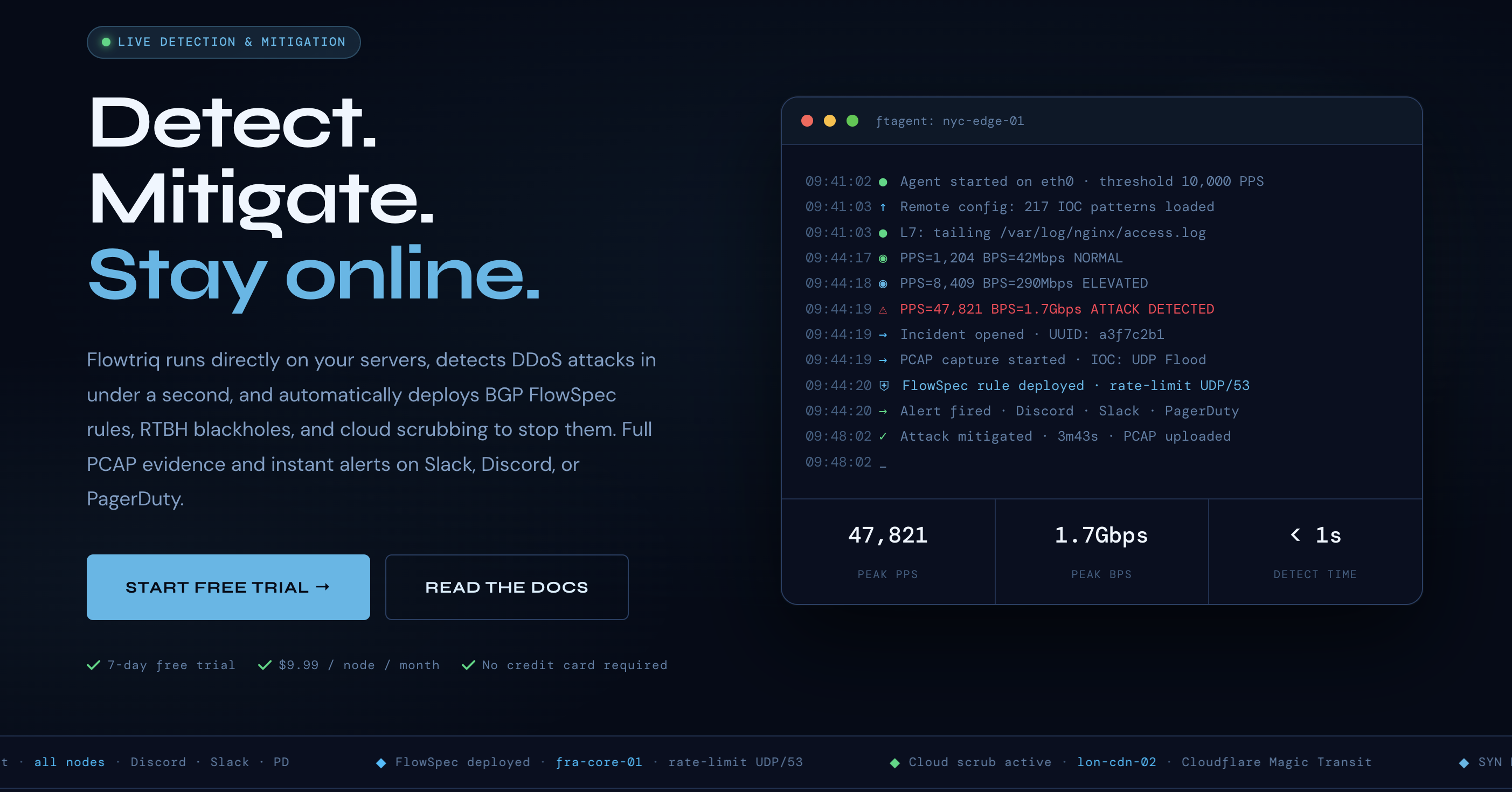
In the next six minutes, you'll learn how to shield your acquisition funnel from the silent conversion-killer: sub-second DDoS latency. I’ve spent the last eight years watching startups crumble because their "unbreakable" infrastructure folded under a basic SYN flood. At Acquisition Arsenal, we view security not as a cost center, but as a weapon for winning and keeping customers. Flowtriq is a lightweight, agent-based powerhouse built on a "detect-and-deflect" philosophy. It bypasses the bloat of traditional hardware appliances by deploying a Python-based agent (ftagent) directly onto your Linux nodes. It reads packets at the NIC level, learns your baseline, and mitigates threats in under a second—all while I’m busy dusting my vintage 1970s Shogun Warriors.
The Zero-Threshold Defense Architecture
Flowtriq moves away from the "set it and forget it" (and then watch it fail) model of static threshold tuning. The architecture is split between a local, high-performance Python agent and a centralized cloud intelligence dashboard. The ftagent isn't just a passive logger; it’s an active observer reading raw packet data directly from the Network Interface Card (NIC). This design decision is critical: by processing at the edge, Flowtriq avoids the latency inherent in backhauling traffic to a scrubbing center before a threat is even identified.
The system scales horizontally by design. Whether you’re running a single game server or a global SaaS edge network, each node reports to the centralized dashboard via encrypted telemetry. This allows for a "herd immunity" effect—if one node sees a new Mirai botnet variant, the entire arsenal is alerted. It’s the kind of proactive stance I wish I had back in 2016 when my first bootstrapped project got knocked offline for three days by a bored teenager with a booter script.
Feature Breakdown: Tactical Superiority
Core Capabilities
- ▸Sub-Second BGP FlowSpec Deployment: When a multi-vector attack hits, Flowtriq doesn't wait for a human. It can automatically push BGP FlowSpec rules to your upstream providers. This effectively "shaves" the malicious traffic off at the edge of the internet before it even touches your rack.
- ▸Dynamic Baseline Learning: Stop me if you've heard this one: a marketing campaign goes viral, and your security software kills the "attack" (which was actually just 10,000 eager customers). Flowtriq’s AI-driven baselining understands the difference between a legitimate traffic spike and a Layer 7 HTTP flood, adjusting its sensitivity in real-time.
- ▸Automated Forensics (Auto-PCAP): This is my favorite "nerd" feature. The moment an attack is detected, Flowtriq triggers a full Packet Capture (PCAP). You get a forensic "black box" recording of exactly what hit you, allowing for post-mortem analysis that actually means something.
Integration Ecosystem
Flowtriq is built for the modern DevOps stack, not some legacy enterprise silo. Out of the box, it chains mitigation steps into "Playbooks"—think of them as automated incident response runbooks. If an attack exceeds a certain PPS (Packets Per Second), the system can trigger a webhook to Cloudflare Magic Transit, fire a high-priority alert to PagerDuty, and drop a notification in your Slack "War Room" simultaneously. It also plays nice with OVH VAC and Hetzner's internal scrubbing, making it a versatile layer for multi-cloud setups.
Security & Compliance
For those of us dealing with sensitive fintech or e-commerce data, Flowtriq keeps a lean profile. The platform maintains an immutable audit log of every mitigation action taken—essential for compliance audits. While the agent is powerful, the data sent to the cloud is metadata-heavy, not payload-heavy, ensuring you aren't leaking customer PII (Personally Identifiable Information) just to stay online. They even offer 365-day PCAP retention for enterprise users who need to satisfy long-tail regulatory requirements.
Performance Considerations
The ftagent is surprisingly nimble. In my testing, the CPU overhead is negligible because it isn't trying to proxy all your traffic—it’s just sniffing it. Reliability is baked into the "fail-open" nature of the agent; if the agent service hangs (unlikely, but I’m a pessimist), your traffic keeps flowing. The sub-second detection isn't marketing fluff; it’s a byproduct of checking PPS metrics every single second, whereas traditional monitors often average out traffic over 30-60 second windows, missing micro-bursts entirely.
How It Compares Technically
In the world of "Acquisition Weapons," you have to choose your blade carefully. Flowtriq is a surgical scalpel compared to the heavy broadswords of the industry.
- ▸Compared to Cloudflare, Flowtriq provides deeper on-host visibility and faster local mitigation for non-HTTP traffic (like UDP game protocols).
- ▸Compared to Fastly, it’s significantly more budget-friendly for bootstrappers ($9.99/node is a steal).
- ▸Compared to Akamai, the implementation time is minutes, not months of professional services.
Developer Experience
The "two-minute install" claim actually holds water. It’s a standard Linux package install, and the documentation is written by people who clearly spend their time in terminal windows, not just in boardrooms. They provide a massive library of free tools, including a BGP FlowSpec builder and an iptables generator, which shows they care about the community. Plus, their research into the Mirai botnet kill switch (CVE-2024-45163) gives them serious "street cred" in my book.
Technical Verdict
Flowtriq is the ideal choice for SaaS founders, game server ops, and MSPs who need "big iron" protection on a "lean startup" budget. Its biggest strength is its speed of detection and the automation of the "oh crap" moment. Its limitation? If you are looking for a purely client-side WAF for a simple WordPress blog, this might be overkill—this is a tool for infrastructure-level defense. If you want to ensure your acquisition funnel never shutters due to a DDoS, Flowtriq is a mandatory addition to your tool arsenal. Just don't ask it to fix your CSS; it's too busy hunting botnets.
Ready to engage with Flowtriq?
[ ENGAGE TARGET ]→